OverflowByte Weekly: Cloud Broke, Kernels Got Exploited, and AI Took Over the Pipeline — May 4–10, 2026
I am a cloud enthusiast and a full time system administrator with passion for designing robust and efficient cloud architectures to empower businesses. As an AWS Certified Cloud Practitioner, I leverage my skills in Windows Server, DNS, Kubernetes, ECS, Route53, Docker, Ansible, KubeFlow, and Linux to create innovative solutions. I'm constantly expanding my knowledge, currently delving into MSSQL and Kubernetes, and staying updated on the latest cloud trends.
Every week I track what actually matters in Cloud, DevOps, Linux, and AI infrastructure so you don't have to doomscroll through a hundred changelog posts. This is OverflowByte Weekly.
This wasn't a quiet week. AWS lost power in us-east-1. Two Linux kernel CVEs landed with working exploits. Kubernetes 1.33 entered its end-of-life countdown. And Google's vision for the "agentic enterprise" started to look less like a keynote slide and more like something you'll be deploying in six months.
Let's get into it.
🔴 Security: Three Linux Kernel CVEs You Need to Act On Today
I'm leading with security this week because this isn't theoretical. These are actively exploited, publicly available exploits. If you manage Linux nodes in any environment — cloud, bare metal, containers — stop and read this section first.
Copy Fail — CVE-2026-31431 (CISA KEV, CVSS 7.8)
Disclosed on April 29, added to CISA's Known Exploited Vulnerabilities catalog on May 1. Federal agencies have a patch deadline of May 15, 2026.
Here's what makes this one scary: the exploit is 732 bytes of Python. That's smaller than most of the error messages I've debugged this year. Any unprivileged process — not root, no special capabilities — can use it to perform a deterministic 4-byte write into the page cache of any readable file on the system. From there, it can surgically corrupt in-memory representations of setuid binaries like /usr/bin/su and escalate to full root without touching the on-disk file.
In a Kubernetes environment, this is a container escape. The page cache is shared across the host and containers, so an attacker already inside any pod — even a non-root pod with all capabilities dropped — can break out to the host node.
The part that stings: your default seccomp profile doesn't stop it. RuntimeDefault blocks socket(AF_VSOCK) but not socket(AF_ALG). AF_ALG is treated as a normal userspace API. Every cluster tested with Pod Security Standards restricted was still vulnerable.
Affected distributions: Ubuntu 20.04, 22.04, 24.04, RHEL 10, Amazon Linux 2023, Debian, Fedora, Arch — essentially everything running kernels built since 2017 (versions 4.14 through 6.18.21 and 6.19 before 6.19.12).
Fix:
# Check your kernel version
uname -r
# Patch target: 6.18.22+ or 6.19.12+ or 7.0+
# Ubuntu
sudo apt update && sudo apt upgrade linux-image-generic
# RHEL/Amazon Linux
sudo dnf update kernel
# Immediate mitigation if you can't patch yet
# Block AF_ALG socket creation via seccomp custom profile
# Or disable the module:
echo "install algif_aead /bin/false" >> /etc/modprobe.d/copy-fail.conf
Red Hat issued RHSA-2026:13565 for RHEL 9 on May 4 addressing this. Azure Linux released 3.0.20260506 with dozens of security fixes. If you haven't applied these, apply them now.
DirtyFrag — CVE-2026-43284 + CVE-2026-43500
Publicly disclosed on May 7, 2026 — this one is fresh. A PoC is already circulating.
Two vulnerabilities, disclosed together. Both allow a local unprivileged user to escalate to root with no special privileges. They're triggered via the xfrm-ESP (IPsec) and RxRPC (AFS) kernel modules.
If you're running IPsec tunnels or AFS clients, this is directly in your path. If you're not, these modules can still be autoloaded in some configurations.
Immediate mitigation while patches roll out:
printf 'install esp4 /bin/false\ninstall esp6 /bin/false\ninstall rxrpc /bin/false\n' \
> /etc/modprobe.d/dirtyfrag.conf
rmmod esp4 esp6 rxrpc 2>/dev/null
echo 3 > /proc/sys/vm/drop_caches
No permanent fix is available yet from most distros at time of writing. Monitor your vendor's security tracker.
Pack2TheRoot — CVE-2026-41651
Disclosed April 22. This one has a different story.
It's a 12-year-old bug in PackageKit that allows passwordless package installation and removal as root. It was discovered with the assistance of AI — specifically, Anthropic's Claude Opus. A vulnerability that lived in production systems for over a decade was caught by an AI tool in 2026.
That tells you two things: AI-assisted security research is real and it's finding things humans missed for years. And your system is probably running software with bugs that are older than some of your junior engineers.
Patch PackageKit now:
# Check your version
pkcon get-distro-upgrades
# Update
sudo apt update && sudo apt install packagekit # Debian/Ubuntu
sudo dnf update PackageKit # RHEL/Fedora
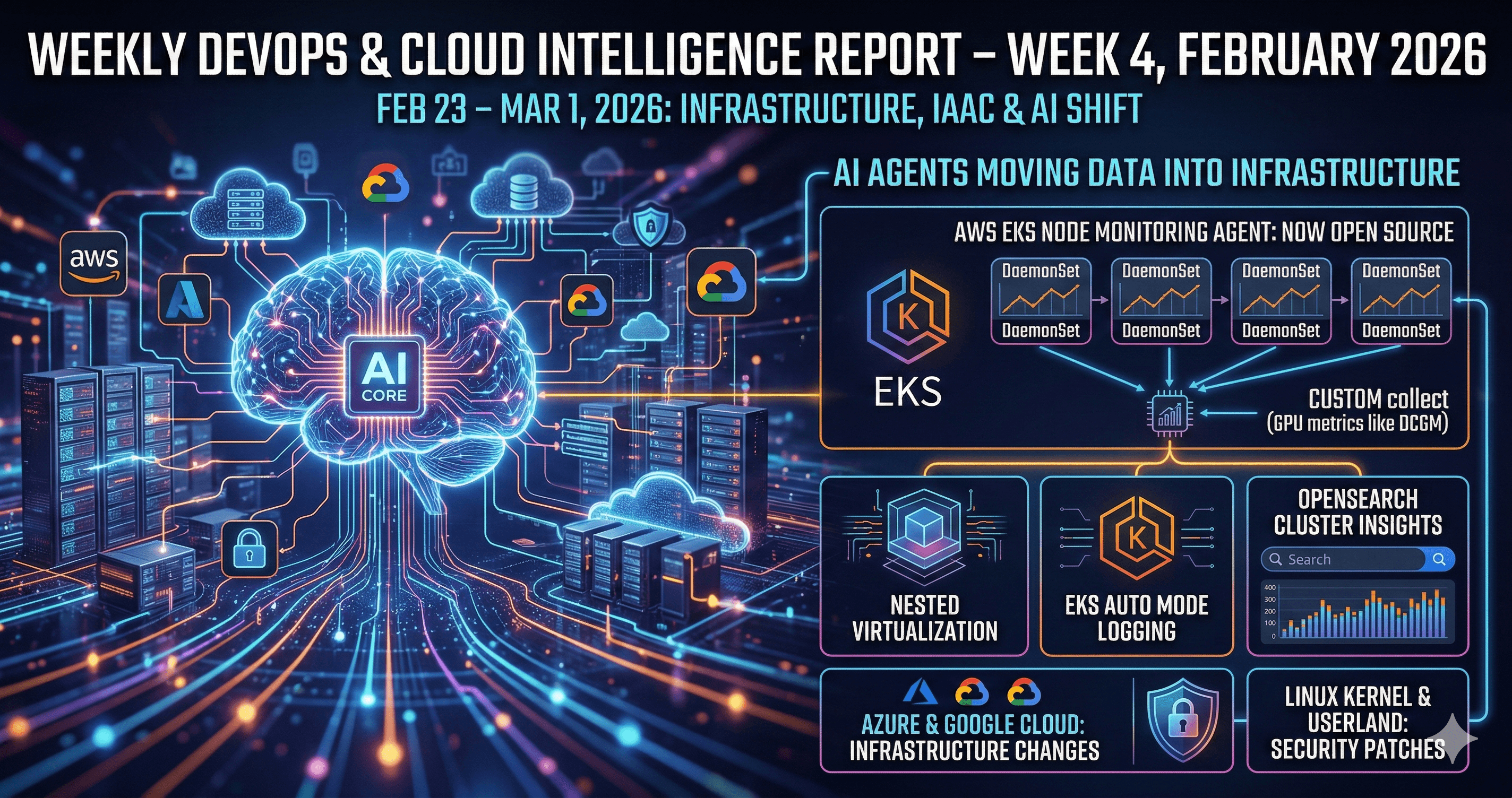
☁️ Cloud & DevOps
AWS us-east-1 Outage — May 7–8
A thermal event at a single Northern Virginia data centre caused power loss, knocking out EC2 instances and EBS volumes in one Availability Zone. Amazon shifted traffic to other AZs, and cooling was restored by Friday afternoon — but a small number of resources remained impaired.
FanDuel, Coinbase, and several other services were disrupted.
Every time an outage like this happens, I see the same debate: "Why weren't they multi-AZ?" And every time, the answer is the same: it costs more, it requires more architecture work upfront, and teams defer it until something like this forces the conversation.
Multi-AZ is not a luxury. It's the baseline. If your production workloads are single-AZ in us-east-1 specifically — which is historically the most incident-prone AWS region — this is the week to fix that.
Azure: What's New, What's Retiring
Now GA: Azure Dld/Eld v7-series VMs powered by Intel Xeon 6 processors. If you have compute-heavy workloads on older VM series, this is worth benchmarking. The performance uplift is real.
In Preview:
cert-managerfor Azure Arc-enabled Kubernetes — finally native cert management for Arc clustersBulk VM restore via Azure Backup — useful for disaster recovery at scale
Application Gateway for Containers as an AKS Automatic add-on
Retiring — mark your calendars:
Azure Reserved VM Instances for select series: July 1, 2026
Azure Document Intelligence v3.0 API: March 30, 2029 (far out, but plan migrations now)
If you're managing Azure costs, audit your reservations before July 1. Unused reservations on retiring series mean wasted spend.
Kubernetes 1.33: EOL is June 28, 2026
Kubernetes 1.33 entered Maintenance Mode on April 28. That means only critical security fixes from here. End-of-Life is June 28, 2026.
Oracle Cloud Container Engine has already added support for 1.33.10, 1.34.2, and 1.35.2 — and will drop support for 1.33.1 after June 8.
If your clusters are running 1.29 or 1.30, you're not just behind on one version. You're accumulating security debt across every component that depends on Kubernetes internals. Plan your upgrade path now. The earlier you start, the less it hurts.
# Check your current version
kubectl version --short
# Check available versions in your managed service
# AKS
az aks get-versions --location eastus --output table
# EKS
aws eks describe-addon-versions --query 'addons[0].addonVersions[].compatibilities[].clusterVersion'
# GKE
gcloud container get-server-config --zone us-central1-a
🤖 AI in DevOps: From Hype to Production Reality
Google Cloud Next '26 — The Agentic Enterprise
The dust from Google Cloud Next 2026 is still settling, but the announcements are significant. A few that will directly impact how we operate infrastructure:
Gemini Enterprise Agent Platform — Google's framework for building, governing, and scaling thousands of AI agents across an organization. This isn't a chatbot interface — it's an orchestration layer for autonomous agents that can take actions across cloud services.
8th-gen TPUs — TPU 8t for training (up to 9,600 TPUs per superpod) and TPU 8i for inference. The hardware is catching up with the ambition of agentic workloads.
Wiz AI-APP (AI Application Protection Platform) — Following Google's $32B acquisition of Wiz, this is the first major integrated product. AI agents doing threat hunting, writing security rules, cutting alert investigation time from 30 minutes to 60 seconds. Not a demo. In production.
Model Context Protocol (MCP) across all Google Cloud services — Google is going all-in on MCP for agent interoperability. If you've been building with MCP, this matters a lot. The protocol is becoming infrastructure.
AI Tooling Moves This Week
Snyk + Claude (Anthropic): Claude models are now integrated into the Snyk AI Security Platform. AI-assisted vulnerability remediation as the default workflow, not a bolt-on.
Opsera + Cursor: DevSecOps agents embedded directly in Cursor IDE. Architecture analysis, security scanning, compliance auditing — all running while you write code. The inner loop and outer loop of development are merging.
Spacelift: AI-enforced IaC policy checking across Terraform, OpenTofu, Ansible, and Pulumi. Drift detection with AI-suggested remediation.
Datadog Watchdog + Dynatrace Davis AI: Predictive incident management is becoming standard. These tools are forecasting failures hours in advance, not just alerting after the fact.
The shift I'm watching closely: AI isn't just observing pipelines anymore. It's acting in them. The DevOps engineer's job is moving from writing automation to governing it.
Red Hat Summit 2026 — Watch This
Kicks off May 11–14. The focus this year is operationalizing AI at scale via OpenShift, OpenShift AI, and Ansible Automation Platform. If you're in the Red Hat / hybrid-cloud space, this week's announcements will matter. I'll cover the highlights in next week's OverflowByte Weekly.
📈 Career Corner: Where the Market Is Moving
Top certifications right now (in demand, verified by hiring patterns):
CKA — still the gold standard for Kubernetes operations
CKS — Kubernetes security, increasingly required for cloud-native security roles
Terraform Associate — IaC is not optional
AWS DevOps Engineer – Professional — end-to-end pipeline ownership
AZ-400 (Azure DevOps Engineer Expert) — strong for Azure-heavy shops
Compensation benchmarks (India, 2026):
Mid-level DevOps: ₹15–25 LPA
Senior / Platform Engineering roles: ₹30 LPA+
Global mid-level average: $110K–$160K annually
What's driving those senior numbers: Platform Engineering. Organizations are building internal developer platforms to abstract infrastructure complexity from application teams. The engineers designing those platforms — with strong IaC, Kubernetes, and increasingly AI-ops skills — are the ones seeing the top of the salary range.
If you're a DevOps engineer asking what to focus on for the next 12 months: CI/CD automation, IaC, container orchestration, observability, DevSecOps, and AI-enhanced operations. In that order. Build depth in the first four before chasing the last one.
🛠️ Your Checklist for This Week
Before you close this tab, here's what actually needs to happen:
[ ] Patch Linux kernels to 6.18.22+ — or at minimum disable AF_ALG, esp4, esp6, rxrpc modules
[ ] Update PackageKit across all managed systems (CVE-2026-41651)
[ ] Check your Kubernetes version — if you're on 1.33, upgrade planning starts now. EOL is June 28.
[ ] Audit Azure VM reservations — select series retire July 1
[ ] Review your AZ architecture after the us-east-1 outage
[ ] Treat any container RCE as a node compromise until Copy Fail is patched
[ ] Watch Red Hat Summit May 11–14 if you're in the hybrid cloud space
Bottom Line
This week was a reminder that the fundamentals don't go away just because AI is everywhere. Power fails. Kernels have bugs. Upgrade windows matter. The engineers who handle these incidents well — and recover fast — are the ones who were already doing the boring work of patching, versioning, and architecture reviews before the incident happened.
The AI tooling is genuinely exciting. But it doesn't replace kernel hygiene.
Stay patched. Stay current.
Found this useful? Share it with someone who manages Linux nodes and hasn't patched yet. They'll thank you later — or they won't, because their cluster will still be running.
Subscribe to OverflowByte Weekly for the next issue. New post every Sunday.